Apple recently launched its iOS 17 update for everyone. Now, all eligible iPhone devices can download the update to finally experience the new features it brings. One of the most talked about features is Live Voicemail, which enables users to transcribe the message in the form of text even as the person who has called you is speaking in real-time. Know more about the iOS 17 feature here and how to enable it on your iPhone.
iOS Exploits Traced to Israeli 'Predator' Spyware Used on Egyptian Politician
22.09.2023 - 20:53 / pcmag.com / Ios
Thursday’s newly disclosed vulnerabilities in iOS were used to install spyware on an iPhone belonging to an Egyptian politician running for president, according to security researchers.
The findings come from spyware watchdog group Citizen Lab, which worked with Google to report the vulnerabilities to Apple earlier this month. On Thursday, Apple rushed out an emergency patch to protect iPhone, iPads, and Macs from the threat.
Citizen Lab says it discovered the vulnerabilities after the Egyptian presidential candidate Ahmed Eltantawy reached out to the organization over suspicions that his iPhone had been compromised. “Our forensic analysis showed numerous attempts to target Eltantawy with Cytrox’s Predator spyware,” Citizen Lab said in the report.
Cytrox is an Israeli-Hungarian cyber arms dealer that sells to foreign governments. The company’s “Predator” spyware was previously documented infecting devices belonging to two exiled Egyptians, along with other targets, including an employee at Facebook’s parent Meta.
In Eltantawy’s case, the attack leveraged three iOS vulnerabilities to secretly install Cytrox’s Predator spyware. Exploiting the vulnerabilities can allow a hacker to booby-trap a website to trigger rogue computer code on an iPhone, elevate their hacking privileges on iOS, and also bypass Apple’s security system to check if an installed app is legitimate or not. The result paves the way for a zero-click attack, requiring no user interaction. Hence, Citizen Lab is urging all iPhone users to patch their devices.
But perhaps the most disturbing finding is how Eltantawy’s own cellular provider played a role in installing the spyware on his phone. Vodafone Egypt forwarded his iPhone’s browser to malicious websites designed to load the Predator payload.
“In August and September 2023, when Eltantawy visited certain websites without HTTPS from his phone, using his Vodafone Egypt mobile data connection, he was silently redirected to a website (c.betly[.]me) via network injection,” Citizen Lab noted.
Google’s own report adds if the malicious c.betly[.]me domain detected that the visitor was the right target, it would then send the user to another site that proceeded to exploit the iOS vulnerabilities to hijack the iPhone.
Vodafone didn’t immediately respond to a request for comment. But the carrier’s suspected involvement is causing Citizen Lab to conclude the Egyptian government itself is behind the spyware attack.
“Given that Egypt is a known customer of Cytrox’s Predator spyware, and the spyware was delivered via network injection from a device located physically inside Egypt, we attribute the network injection attack to the Egyptian government with high confidence,” the group added.
To
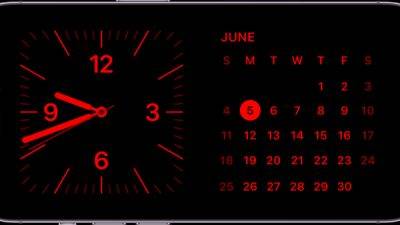
StandBy Mode in iPhone: Know how to unlock and use this amazing iOS 17 feature - just tilt
After the launch of the iPhone 15, Apple rolled out its newest software update for iPhones, that is, the iOS 17. With this update, Apple has brought many exciting features and one of them is the StandBy Mode. Have you used this feature yet? Know all about this it and learn how to use it.

Keywords Studios' unionised Dragon Age QA team laid off
Dublin-based Keywords Studios has laid off its Dragon Age: Dreadwolf QA team contracted to assist BioWare Edmonton in Canada.

Honkai: Star Rail Fu Xuan Trace Guide
Fu Xuan is a Quantum Support character who specializes in damage splitting and healing. Introduced during the first portion of the Xianzhou Luofu Trailblaze Mission, Fu Xuan recently became playable with Version 1.3 of Honkai: Star Rail.

Resident Evil Village iOS Launches Just In Time For Halloween
The iPhone and iPad will be extra spooky this October.

Starfield update patches out loot exploits, 'larger update' with DLSS support, FOV slider still in the works
An update for Starfield has been released today, but temper your expectations: the patch is a small one aimed at closing some exploits and fixing a few bugs. The other stuff players have been waiting for, like the missing FOV slider and brightness controls, DLSS and ultrawide monitor support, and city maps, still haven't arrived.

Got your new iPhone 15? Now, know how to use Live Stickers courtesy iOS 17
In the ever-evolving world of technology, Apple has once again pushed the boundaries with its latest iOS 17 update. It was rolled out on the iPhone 15 series and a few days later, the software was released for all iPhone users. The iOS 17 was announced in June, but the final software version was made available to users on September 18. Before that, only the beta version of iOS 17 was there for developers and testers. Among its many exciting features, is one called Live Stickers. It is such a fun and exciting feature that users, young and old, are going crazy about its ability to push innovation to an ever higher level. Know what exactly Live Stickers feature is and how it is used.

Live voicemail: Apple dropped the most amazing iOS 17 feature! Know how to use it
Just after the grand ‘Wonderlust event' Apple rolled out its most awaited iOS 17 on September 18 for most iPhone users. It has brought some amazing features with its final upgrade. iOS 17 was announced in June and since then only beta updates have been available. Now that it is finally here, the interminable gap between the announcement and the actual rollout, is much more acceptable simply because of the huge changes and benefits made available to all by Apple. Users are quite excited now that it is finally here. One of the many mind-blowing features of iOS 17 is Live Voicemail. This is a revolutionary feature that can save you from a lot of unwanted calls that usually end up wasting time or leaving you stressed and frustrated. Know what this iOS 17 feature is all about.

Using Quick Start to Set Up an iPhone 15? You'll Need to Update iOS 17 First
If you purchased an iPhone 15 this week, and are looking to automatically transfer data from an older iPhone to your new one using Quick Start, you’ll need to update the iPhone 15 first.

Yikes: Apple Patches 3 New Zero-Day Exploits for iOS, MacOS
Apple today released a fix for a trio of iOS vulernabilities that hackers may already be exploiting.

Heavily Modded Starfield With ReShade Ray Tracing and DLSS 3 Looks The Part
YouTuber and artist 'Digital Dreams' has released a new video, showing off a heavily modded Starfield with over 50 mods and the artist's custom ReShade Ray Tracing shader.

Top 3 iOS 17 features that you should enable on your iPhone now
iOS 17 was released yesterday for iPhone users around the world, and it brings several new features to iPhones, in addition to bug fixes, and performance improvements. Apple, at its World Wide Developers Conference (WWDC) 2023, announced its next big update for iPhones, with new features such as StandBy, Contact Posters, Journal app, and more. However, there are several more features that were not given as much attention time on the stage by the top Apple executives but these can take your iPhone experience to the next level.
